#testenfürdenwinter - 30% günstiger!
Wir reduzieren ab sofort die Preise unserer Penetrationstests und Schwachstellenanalysen um 30% für alle Unternehmen und Organisationen, die täglich unsere überlebenswichtige Infrastruktur in Deutschland am Leben halten.
Why vulnerability management?
60 percent of all successful attacks are the result of exploiting a vulnerability for which a patch already existed at the time of the attack.
Consistently recognizing and eliminating technical vulnerabilities is an effective measure to protect against cyber attacks of any kind.
If companies’ IT systems are successfully compromised by attackers, the costs of the consequences usually run into the hundreds of thousands.
High costs, long downtimes: Cyber attacks can threaten the existence of small and medium-sized companies in particular.
Therefore, look at the weaknesses of your IT infrastructure through the eyes of a potential attacker. Only by continuously carrying out vulnerability tests will you be able to objectively assess and improve the resilience of your infrastructure.

What is VMaaS?
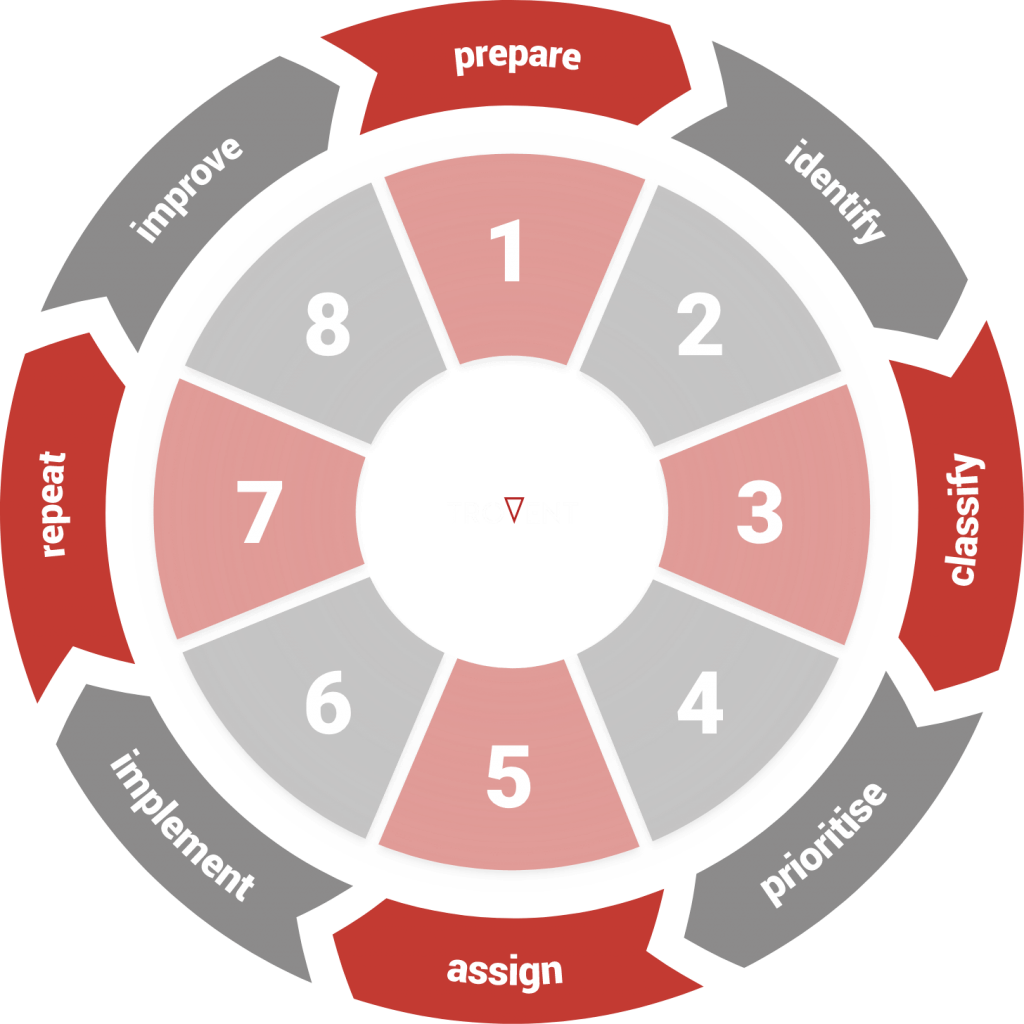
Professional vulnerability management does not end with detection! It also extends to remedying the respective vulnerability and monitoring the results.
With Trovent VMaaS – Vulnerability Management-as-a-Service – you get comprehensive vulnerability management as a service provided by us.
Trovent VMaaS: What does it offer in detail?
Trovent Vulnerability Management is more than a one-off scan of the IT infrastructure! And it is also more than a penetration test, which only ever focuses on certain parts of the infrastructure and whose results quickly lose their relevance over time.
We provide you with an overview of all the technical vulnerabilities to be found in your company’s IT/network infrastructure and web application landscape. In this way, we ensure complete visibility of the attack surface of your IT infrastructure.
Trovent VMaaS enables:
- Immediately detect known and newly published vulnerabilities.
- To Fix vulnerabilities in a targeted manner.
- Identify system misconfigurations.
- Identify services that are not required.
- Verify improvement measures that have already been implemented.
- Check and regularly update asset management and configuration databases.
Vulnerability management as a comprehensive service
We always deliver vulnerability management as a combination of technology and service (“as a service”). Trovent VMaaS thus serves as a solid foundation for an effective vulnerability management process in your company.
How does your company benefit from Trovent VMaaS?
From the information security officer to the management: The biggest advantages of Trovent VMaaS from different perspectives.
Knowledge of the potential attack surface
An up-to-date overview of the actual vulnerabilities of the company’s entire IT infrastructure at all times.Reduction of the information security risk
Thanks to the detection of vulnerabilities, targeted improvement measures can be implemented to keep the information security risk at a continuously low level.Immediate delivery capability
No lengthy implementation phase. After setting up the scan profiles and installing the scan appliances as virtual machines, the vulnerability management service is immediately ready for use.Focus on core competencies
Trovent VMaaS allows internal IT to focus on its core competencies as the vulnerability management process is outsourced to an external specialist.Access to experienced experts
Trovent VMaaS is ready to use immediately, without the lengthy and costly process of setting up dedicated internal positions.Efficiency and increased productivity
The flood of false positives is avoided and the focus is placed on actually relevant vulnerabilities. Trovent VMaaS enables the implementation of an efficient vulnerability management process without burdening the existing IT department.Easy integration capability
Using existing interfaces, the Trovent VMaaS scanning platform can forward the results or reports to existing IT service management/ticketing systems. The same applies to the integration of the service into existing security operations processes.100% European solution
Trovent VMaaS is hosted in an ISO 27001-certified data center in Sweden. The service is provided exclusively from Germany. Sensitive information about detected vulnerabilities in the IT infrastructure remains under Trovent’s control in Germany and Sweden.
- Objective assessment of vulnerability
Trovent VMaaS creates the technical prerequisites for being able to make a valid statement as to whether and to what extent the IT infrastructure is vulnerable. - Minimization of additional costs
There is no need to set up a lengthy and cost-intensive internal team to specifically identify and eliminate vulnerabilities. - Increased resilience
The technical attack surface is eliminated in a targeted manner, significantly reducing the potential for attackers. - Protection of important information assets
The elimination of vulnerabilities enables the protection of business secrets, confidential customer data, intellectual property and personal data. This effectively prevents reputational damage. - No dependence on the service provider
It is possible to work towards independent operation of the vulnerability management infrastructure and processes.
- State of the art
The ‘state of the art’ required in Art. 32 GDPR is demonstrably used to “…ensure the confidentiality, integrity, availability and resilience of the systems […]”. - Immediate overview of the attack surface
Possible threats to confidentiality and integrity can be detected at an early stage with Trovent VMaaS. - Avoid crises
Functioning vulnerability detection processes enable the consistent reduction of the attack surface. They minimize the probability of a crisis occurring, for example the loss of personal data. - Prevention of reputational damage
By identifying and eliminating vulnerabilities, the probability of losing business secrets, confidential customer data, intellectual property and personal data is massively reduced. This minimizes the risk of reputational damage.
- Assessment of the initial situation
Thanks to Trovent VMaaS, objective statements can be made about the risk to the IT infrastructure and information security. - Basis for risk analysis
A functioning risk assessment in accordance with ISO 27001 or IEC 62443 and other standards requires you to proactively identify your weak points in order to be able to assess and quantify risks. Trovent VMaaS creates the basis for this. - Compliance with industry-specific standards
The consistent identification and elimination of vulnerabilities in a standardized process supports the implementation of the “state of the art” required by various information security standards and laws.
Test Trovent VMaaS without obligation

Are you interested in our vulnerability management solution?
Would you like to see it in action in a real environment?
We would be happy to demonstrate the performance of our solution in your IT infrastructure!
Contact us and we will arrange the framework conditions for the test deployment as quickly as possible.
We will gladly advise you
Do you see a need for action in your IT security architecture?
Would you like to implement improved vulnerability management or an attack detection solution in your company?
Would you like to talk to an expert on the subject of cyber security?
We will be happy to provide you with a free consultation.